AI-Powered Notification Summaries on Pixel Phones: Activation and Privacy Risks
A Brief Overview of AI-Powered - AI-powered notifications on Pixel devices - Google Pixel smartphones introduce a new and exciting feature to their users called AI-generated notification summaries. This innovation aims to further enhance the user experience by displaying notifications on the lock screen in a more concise and easily understandable format.
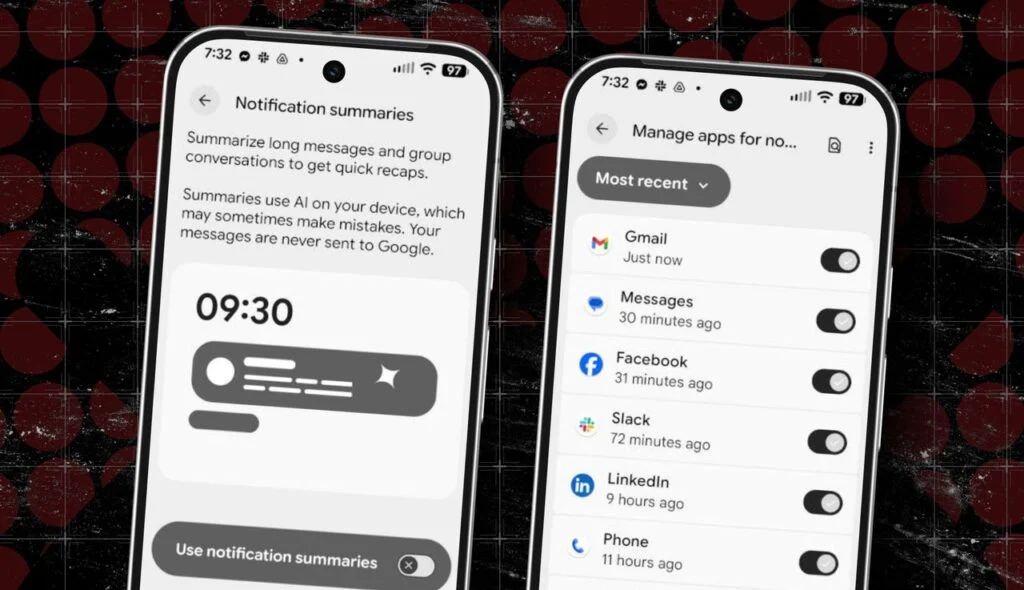
This feature primarily converts notifications from various applications into a brief and concise summary. As a result, users can quickly access important information without even needing to unlock their phones. This is a particularly useful innovation for people with limited time.
There are certain requirements to activate notification summaries. Users must adjust AI-related functions or lock screen notifications in their phone settings. The exact activation steps may vary depending on the device's software version.
However, alongside this convenient feature, there are also some important warnings. One of the most serious issues is the potential privacy risk. The processing of notifications by Artificial Intelligence raises questions about how personal data is managed.
Privacy concerns relate to what data AI accesses when analyzing notification content and how this data is stored. Although Google states that it processes this information only on the device, users are advised to be cautious.
For this reason, Pixel users should carefully review privacy settings and assess potential risks before activating this feature. Data security should always be a top priority.
In conclusion, while AI-powered notification summaries on Google Pixel are a useful innovation, it is important for users to strike a balance between convenience and data security. While leveraging the capabilities of technology, the protection of personal data must always remain paramount.
